Aria stories - Page 94
Aria is where cutting‑edge technology, security, and AI‑driven innovation intersect. The stories tagged here span everything from next‑gen cloud and data platforms to ransomware trends, smart infrastructure, and the fast‑evolving world of generative and agentic AI. If you want to understand how tools like AI copilots, LLMs, and real‑time analytics are reshaping everything from finance to healthcare to manufacturing, this is your starting point.
Dive into in‑depth coverage of cybersecurity – botnets, ransomware variants, mobile malware, zero‑day exploits, and the shift to continuous, intelligence‑led defence. Explore how data centres, networks, and observability platforms are being redesigned for AI workloads, sustainability, and hybrid cloud. Follow the rise of AI in everyday products too, from wearables and smart home devices to vehicles, retail experiences, and next‑gen collaboration tools.
Aria isn’t just about the technology itself, but about its impact: on regulation, trust, jobs, skills, and digital resilience. Here you’ll find expert commentary, major vendor announcements, case studies, and long‑form explainers that help you connect the dots between infrastructure, security, AI, and real business outcomes. If you’re responsible for strategy, architecture, risk, or innovation, the Aria tag will keep you ahead of what’s coming next.
APAC malware and botnet threats charge ahead rest of the world

How the University of Melbourne's data backup puts consolidation front and centre

Exclusive: Ransomware isn't hard to beat - here's how

It's time to move on from “what is the Internet of Things” discussion if you want to secure it

How to be the cat - not the mouse - in the fight against zero-day malware

Ransomware: Expert advice on how to keep safe and secure

Go Phish – how to spot a ransomware email

Proofpoint uncovers new MarsJoke ransomware, then Kaspersky finds the fix

Symantec detects ransomware variants created directly on mobile devices

Google's data center security and design best practices
Planning crucial to minimising and recovering from ransomware
Google to roll out enterprise-class testing and personalisation product
Connected homes and IoT driving residential security systems

Hands-on Review: Microsoft Surface Book a 'pretty special piece of gear'

Unit 42 discovers Komplex trojan targeting OS X systems

Eaton showcases latest power solutions for data centers at DCD '16
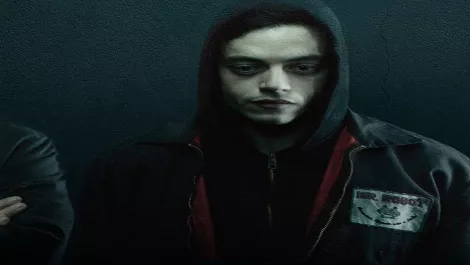
10 cybersecurity lessons learned from Season 2 of Mr. Robot

Carbon Black discovers new adware related threat

Employees download new malware every four seconds, says Check Point
