HID stories - Page 45
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Conspiracy looms: NSS Labs takes CrowdStrike, ESET, Symantec & AMTSO to court

Exclusive: The white hat hackers making sure your internet stays safe

Gartner names Sophos leader in Unified Threat Management

Brewery breach: Not even beer is safe from ransomware

Why the Lazarus group poses a massive threat to businesses

Survey: Rising role of IT in physical security provides opportunities

Secureworks opens up proprietary UEBA through partner programme
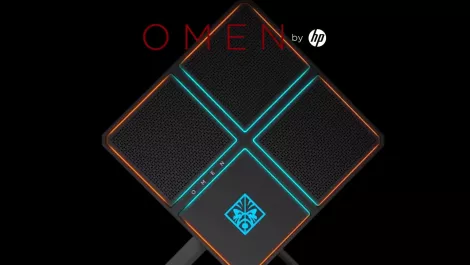
Hands-on Review: HP Omen X PC 900-070a - a gamer's dream

Cryptomining and IoT attacks gunning for healthcare industry

Avaya and Unisys partner to bring cloud-based UC to Aussie Govt

Gigamon partners with Endace for improved network visibility

Former Google exec joins HubSpot as APAC managing director

The best VPNs: How to safely transfer files

Deep dive: Research finds new links among North Korea's malware families

Exclusive: Tackling the challenges faced by women in cybersecurity

Benelux security distributor DCB to operate as part of Nuvias Group

Interview: HID Global on trusted identities in the age of smart buildings

Hands-on Review: Plantronics BackBeat GO 605 headphones

Hands-on Review: No Man's Sky Next adds new features
