The Ultimate Guide to Physical Security
A curated Asian edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Physical Security.
What to know about Physical Security
Physical security encompasses the measures, technologies, and practices designed to protect people, assets, and physical environments from harm, theft, or unauthorized access. This domain integrates hardware like surveillance cameras, access control systems, and biometric verification, with evolving digital solutions such as cloud-based management and AI-powered analytics. Understanding physical security is crucial for safeguarding corporate offices, critical infrastructure, healthcare facilities, and public spaces.
Our collection of stories highlights the dynamic intersection of physical security with digital innovation. Readers will find insights into new security camera technologies, cloud-managed systems, unified identity management, and how AI is transforming surveillance and access control. Additionally, we explore the increasing need to merge physical and cybersecurity practices to address modern threats comprehensively.
Delve into case studies on advancements in workplace optimisation through physical security tools, the importance of hardware security keys for multi-factor authentication, and emerging responses to vulnerabilities in legacy systems. This hub offers a comprehensive look at how organisations are enhancing safety, compliance, and operational efficiency through integrated, state-of-the-art physical security strategies.
Asian Physical Security News
Regional stories with direct local relevance
KnowBe4 expands Asia push amid rising email threats
Rising email fraud is driving KnowBe4's regional expansion, as security chiefs warn that AI-made attacks are targeting Asia's businesses.

Emtek expands Google Cloud AI tools for media production
The rollout should cut production costs further after VidioGen helped Emtek reduce redevelopment time by 30% on an animated series.

Singapore firms urged to loosen AI identity controls
Singapore companies face rising cyber risk as AI agents and machine accounts gain access without proper oversight, Delinea research shows.

Nanomade demos force sensors to Taiwan electronics makers
Finished-product demos in Taiwan could help device makers add pressure-sensitive controls to metal and glass without redesigning hardware.

Dragos appoints Japan Country Manager to expand market
Japan’s industrial operators face rising cyber risk as Dragos formalises local leadership with a first Country Manager appointment.

GITEX AI Asia returns to Singapore amid investment surge
GITEX AI Asia returns to Singapore, drawing 550+ tech firms and 250 investors managing over USD $350 billion amid an AI investment boom.
Analyst Insights
Research and market analysis connected to Physical SecurityHyland named Leader in Gartner's 2026 document review

Rubrik launches Google Cloud tools for AI governance

Kong launches Agent Gateway for multi-agent AI traffic

Protegrity launches AI Team Edition for secure inferencing

Capsule Security raises $7 million to guard AI agents
Featured News
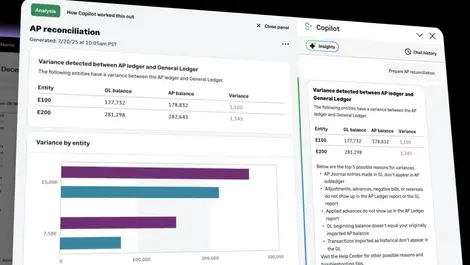
Sage Intacct builds explainable AI into accounting
Accountants facing staff shortages may gain faster workflows, as Sage Intacct’s new agent exposes its calculations, sources and audit trail.

Exclusive: Google Cloud accelerates shift to agentic data
Enterprises may soon design data systems for AI agents rather than staff, as Google Cloud adds real-time context, automation and cross-cloud access.

Netskope's Tony Burnside - visibility is key to AI security
AI tools are creating hidden east-west traffic that security teams struggle to monitor, raising the risk of data leakage and compromise.

Affirmo: Could AI make a reality of IoT dreams?
AI could help unlock the long-promised value of IoT, as Singapore-based Affirmo pushes real-time tracking into manufacturing and logistics.

Rise of AI Agents introduces new infosec risk: Okta
Okta warns that surging numbers of uncontrolled AI agents pose a major identity and access risk as they become the new digital workforce.
Expert Columns

The Death of the Firewall

Digital identity: How it powers APAC's fintech boom

Why service desks are emerging as a critical security weakness

Stolen credentials don't have to mean a breach

One click can trigger a breach, but security can stop it

World IP Day: Why IP is the backbone of sporting brands' success

VPN vulnerabilities don't have to become breaches

Proof beats promise: The trust crisis AI is creating
Building security outcomes for small businesses: Why breaches persist despite available tools

The why and what of FIPS 140-3 validation in modern cybersecurity
Interviews
Interviews and video coverage from the networkRecent Physical Security News
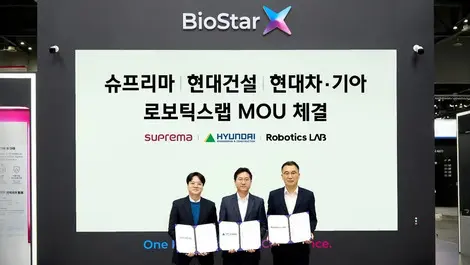
Suprema & Hyundai teams plan robot-ready smart homes
Suprema and Hyundai are teaming up to design AI-secured robot-ready housing, blending architecture, security and autonomous services.
Vietnam fake account farms fuel global cybercrime wave
Vietnam-based fake account farms are fuelling a growing global cybercrime market, flogging cheap logins, bot tools and disposable email tricks.

McCann Singapore teams up with Adobe to extend GenAI
McCann Singapore partners with Adobe to embed generative AI in live client work, boosting brand-safe creative speed, control and measurement.

Blackwired & NTT Japan launch ThirdWatch in market
Blackwired teams with NTT Japan to launch AI-driven ThirdWatch threat intelligence platform for pre-emptive cyber defence in Japan.

Blackwired, NTT Security Japan partner on cyber intel
Blackwired teams with NTT Security Japan to embed its ThirdWatch intel platform in managed services, boosting pre-emptive cyber defence.

Keeper expands PAM distribution with Ingram in Singapore
Keeper deepens its Ingram Micro alliance in Singapore, extending KeeperPAM to more partners amid rising identity-based cyber attacks.

Phishing & smishing scams surge across Philippines
Phishing and smishing scams in the Philippines surged in 2025, with phishing sites jumping 423% as fraud shifts to mobile and social media.

Oracle NetSuite unveils AI-centric NetSuite Next in UAE
Oracle NetSuite unveils NetSuite Next in the UAE, embedding AI assistants, agentic workflows and analytics across its cloud ERP suite.

Indosat's AI spam shield blocks scams worth USD $500m
Indosat's AI spam shield blocked 2bn risky contacts in six months, averting scam losses of about USD $500m for Indonesian users.

Zyxel Nebula 19.30 boosts MSP multi-tenant control
Zyxel updates Nebula to 19.30, adding cross-org multi-tenant tools, RBAC and site cloning to streamline MSP network management at scale.

Zyxel unveils Nebula 19.30 for advanced MSP management
Zyxel has launched Nebula 19.30, adding cross-organisation multi-tenant tools, MSP portal upgrades and USG LITE 60AX router integration.

Check Point backs Google Cloud to close ASEAN 'Cloud Gap'
Check Point backs Google Cloud tools to close ASEAN's 'cloud gap', promising in-band, AI-driven security without slowing digital growth.

Suprema unveils dual BioStar platforms, new biometrics
Suprema debuts twin BioStar access platforms and flagship AI facial terminal at Intersec 2026, targeting high-security, high-traffic sites.

ADLINK wins seven Taiwan awards for AI edge systems
ADLINK has scooped seven 2026 Taiwan Excellence Awards, underscoring its push into AI edge platforms for factories, transport and hospitals.

A-FLOW opens ML1 data centre to power PH digital boom
A-FLOW has launched its ML1 data centre in Laguna, the first phase of a planned 36MW campus to support the Philippines' digital surge.

HID unveils facial recognition readers to secure smart buildings
HID has launched Amico facial recognition readers for smart buildings in Southeast Asia, enhancing secure, contactless access with digital identity integration.

Asia's video security enters a new era of hybrid intelligence
Asia's video security is shifting to hybrid intelligence, blending cloud innovation with existing systems for flexible, scalable monitoring solutions.

Kay Pang Law Practise launches in Singapore for tech startups
Kay Pang Law Practise launches in Singapore, offering tech startups access to senior legal guidance for compliance, governance and growth support.

Quantum, agentic AI & Web 4.0 to transform cybersecurity
Quantum computing, agentic AI, and Web 4.0 will revolutionise cybersecurity by 2026, demanding new strategies for autonomy, threat defence, and infrastructure resilience.
Suprema unveils BioStar X for unified AI biometrics & security
Suprema launches BioStar X, an AI-powered platform unifying biometric access and video surveillance for seamless, scalable security management.
