HID stories - Page 52
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Kaspersky CEO rubbishes 'false' allegations of hacking from US media
Gartner shares five step plan for a successful data center migration
Locky ransomware is back as one of September's 'most wanted' malware

The Coinhive cryptocurrency miner - more trouble than it's worth?

MYOB tackles gender inequality with Male Champions of Change STEM

Security versus convenience? Don't trust everything 'UC'

Salesforce cloud tech helps banks fix customer loyalty problem
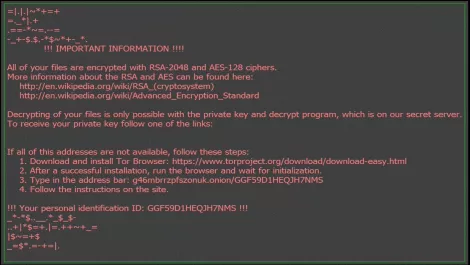
Locky ransomware variant mimics Konica Minolta copier emails

Credential theft is the hottest trend for cyber attackers in Q2

Hands-on Review: Fortnite Battle Royale mode

What's ahead for ransomware: Seven predictions about its evolution

Vexata emerges after 3 years in 'stealth mode' to launch revolutionary product

New wave of Locky ransomware appears to come from Vietnam

Securing the printing process for a revolution in ID card management
5 data centre infrastructure management myths debunked

Quann & Claroty strengthen Singapore's critical infrastructure security

ExpensiveWall signs users up to fraudulent SMS services

6 months under siege: the malware story so far in 2017

Windows 10 security solutions powerless against 'bashware'
