HID stories - Page 53
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Gemalto hails future of biometrics in ePassports for more efficient travel

Gender pay gap should be a social & economic priority, says WGEA

Cobian RAT author crowdsourcing malware botnet distribution

Avaya ANZ expands local reach with new appointments

Review: Knack 2 is a surprising improvement over the original

Are we letting the data race cloud our judgement?

Enterprise security: The hidden perils of 'unguarded talk'
Hands-on Review: Norton WiFi Privacy
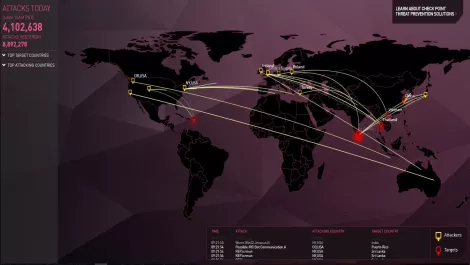
Check Point's latest threat research taken from data you can see in real time

How to drop complexity and move to a more efficient security strategy

Webroot takes over Securecast in move to take cyber awareness training to mass market

Interview: HID Global talks trusted identities, privacy & why we need to be ready for smart buildings

FireEye data leaks continue - or are the hackers just trolling?

Cybercrime: What to expect for the rest of 2017 and how to prepare

Zscaler reports spike in malware families abusing SSL/TLS encryption as part of infection chain

Securing your unified communications: Three key considerations

Review: Nioh's Defiant Honor expansion will keep challenging players

The Dark Web: Is your company at risk?

Equinix, Digital Realty, China Mobile...the vendors fuelling the colocation market
